routers
US
・UK
A1 初級
n. pl.名詞 (複數)路由器
影片字幕
網際網路的黑暗面! (The Dark Side of the Web)
- to download to be able to access this network of onion routers. Today, millions of people
他的意思是,若要做到在網路上真正的匿名 那就必須將技術提供給大家,而非只有美國政府使用
- TOR stands for the Onion Router and is the software you need to download to be able to access this network of onion routers.
如今,世界各地已有數百萬人因為各種用途使用Tor
什麼是網路中立性?為何它如此重要?[完整影片 - 多國語言字幕] (What is Net Neutrality and why is it important? [Full Video - Multilanguage Subs])
- On the crossroads of these streets are routers, which direct the data packets on the right route to their destination.
中立的網路不會根據傳送者、內容、接收者 對資料封包做出任何區別
- The routers don't care who comes down the road, nor do they care how they look, where they are from, where they want to go, or what content they have with them.
不會根據傳送和接受者支付的價格 做出任何區別
SANS Stormcast 4 月 18 日:Remnux 雲端環境;Erlang/OTP SSH 漏洞;Brickstorm 攻擊... (SANS Stormcast Friday, April 18th: Remnux Cloud Environment; Erlang/OTP SSH Vuln; Brickstorm Ba…)
- hello and welcome to the friday april 18th 2025 edition of the sands internet storm centers stormcast my name is johannes ulrich and today i'm recording from orlando florida today we got another guest diary by one of our undergraduate interns jacob clay camp did write about how to get started in malibu analysis of course we have plenty of diaries always about malibu analysis didier and xavier most notably are heavily contributing to this this is more the beginners view of malibu analysis and sort of how to get started with malibu analysis using a cloud-based system a couple interesting parts here first of all jacob is using aws a free instance and then uses chasm workspaces in order to essentially get a remote desktop into a container which then runs remnux this is lenny seltzer's reverse analysis environment all of this is linux-based and since it is set up in a container it's also easy to reset and the cloud deployment of course makes it nice and isolated from anything that you may have going on in your home network overall interesting setup and then jacob is going over a quick analysis of a red tail sample and how to apply this particular environment to the analysis of this particular matter interesting a write-up and nice step-by-step guide to help you get started and then we have a critical vulnerability affecting the erlang otp ssh library this affects any ssh servers written in this language the vulnerability was found by researchers at the ruhr university city in bochum now the otp here in erlang otp does not stand for one term one-time password instead it does stand for the open telecom platform this particular version of erlang was created and maintained initially by ericsson and is often used in telecom related devices routers and the like so certainly there is quite a number of affected devices out there the cbss score of the vulnerability is a perfect 10.0 because it does allow for arbitrary code execution without authentication the problem is that some ssh messages some ssh protocol messages can be sent and executed before authentication finishes due to this bug and that then leads to execution now the user this this code executes at depends on the user the ssh server is running at at the time it receives these messages definitely upgrade but of course since this is a vulnerability in the library used to create the ssh server you may have to wait for respective vendors to actually release updates here in the meantime the only alternative you have is to disable or firewall the ssh server and belgium security company inviso did release a report with details regarding some of their recent findings of the brickstorm backdoor brickstorm has been used in linux in in sort of vmware environments but now they also found a version of this backdoor on windows there are a couple interesting things to note here unlike most backdoors this backdoor actually does not have a remote code execution capability they say that typically rdp and such is used instead by the attacker and that they specifically didn't include a remote code execution capability to evade some heuristic and behavioral detection that you often find that would flag any code execution behavior instead this particular backdoor is able to read write files from the file system it also has some network components that would allow an attacker to essentially use an affected system as a pivot to scan other systems in the network so certainly a capable piece of malware also interesting as a command control channel they're using cloud flare workers and similar systems that again are less likely going to trigger alerts interesting report and it also includes some good indicators of compromise and the ways and techniques how you can actually find if you are affected by this particular backdoor and openai released its latest greatest model gpt 4.1 but this didn't happen amid some controversy around the security aspects here first of all this model was released without the usual safety reports or system cards which typically outline how this particular model was created to be safe meaning not for example allowing to create malware and apparently some of these safeguards that you often find in these models are missing from gpt 4.1 making it trivial to create malware with this model interesting problem here and not even sure if this will be something that the openai will fix in short notice but definitely we have seen malicious models of course before but not from major vendors like openai well that is it for today so thanks again for listening and thanks everybody who i met here i mean all of you listeners at the event here in orlando and well i'll talk to you again on monday bye
大家好,歡迎收聽2025年4月18日星期五的金沙互聯網風暴中心風暴播報,我是約翰尼斯-烏爾裡希,今天我在佛羅里達州奧蘭多錄製節目。當然,我們有很多關於Malibu分析的日記,其中Didier和Xavier的貢獻最大,這篇日記更像是Malibu分析初學者的觀點,以及如何使用雲系統開始Malibu分析。首先,Jacob 使用 aws 免費實例,然後使用 Chasm 工作區,以便將遠程桌面接入容器,然後運行 remnux,這是 Lenny Seltzer 的反向分析環境。當然,雲部署使其很好地與家庭網絡中發生的
- This particular version of Erlang was created and maintained initially by Ericsson and is often used in telecom-related devices, routers, and
HUB、Switch、Router 傻傻分不清楚?一篇搞懂它們的差異! (Hub, Switch, & Router Explained - What's the difference?)
- Now here is an expanded view of routers over the internet.
這裡有不同的數據包,用不同的顏色表示,代表不同的 IP 地址。
- Now here is an expanded view of routers over the internet.
現在,我們來擴展一下互聯網路由器的視野。
二層交換機 vs 三層交換機:該怎麼選? (Layer 2 vs Layer 3 Switches)
- Now, it could use a router to do this, because routers route by IP addresses.
現在,他們可以用路由器來做到這點,因為路由器是根據 IP 位址來路由的。
- Now, it could use a router to do this, because routers route by IP addresses.
但一個更好、更簡單的方法是使用 layer 3 switch。
行動裝置連線教學|CompTIA A+ 220-1101 考題解析 1.3 (Connecting Mobile Devices - CompTIA A+ 220-1101 - 1.3)
- You can probably still find devices in your infrastructure that use DB9 connections with RS-232 to be able to connect and view consoles on switches, routers, and other devices.
您可能還能在基礎設施中找到使用 DB9 連接和 RS-232 的設備,以便連接和查看交換機、路由器和其他設備上的控制檯。
- You can probably still find devices in your infrastructure that use DB9 connections with RS232 to be able to connect and view consoles on switches, routers, and
您還可以將 NFC 用作門禁設備或類似身份證的東西,您可以將其舉到傳感器上,用它來打開電子門鎖。
TCP/IP 與 OSI 是什麼? // 免費 CCNA // EP 3 (what is TCP/IP and OSI? // FREE CCNA // EP 3)
- The network layer, all about IP addresses and routers.
這其中有很多因素。
- So for example, the physical layer, we know that's going to involve ethernet cables, the network layer, all about IP addresses and routers.
例如,物理層,我們知道這將涉及以太網電纜,網絡層,所有關於 IP 地址和路由器的內容。
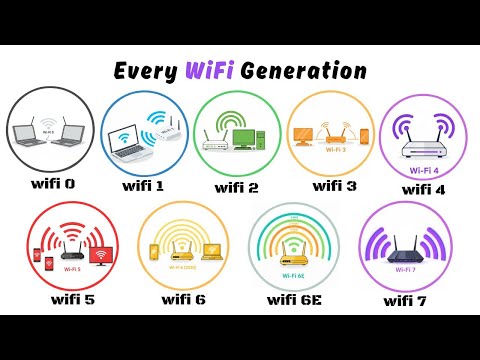
一次搞懂所有 Wi-Fi 世代!6 分鐘帶你看懂網速進化史! (Every Wi-Fi Generation Explained in 6 Minutes)
- routers within a few meters of each other.
路由器在幾公尺內。
- and routers within a few meters of each other.
它使用了 5 GHz 頻段而非 2.4 GHz,提供了高達 54 Mbps 的更快數據傳輸速率。

![什麼是網路中立性?為何它如此重要?[完整影片 - 多國語言字幕] (What is Net Neutrality and why is it important? [Full Video - Multilanguage Subs])](https://img.youtube.com/vi/HCUg5A-ZAw0/hqdefault.jpg)